Password [new]: Kmsauto Net 2016 V 1.4 9 Portable
In the attic, the laptop still hummed, now displaying a simple message: “The Last Key is not a password—it is the willingness to share.” Maya smiled, knowing that the real activation had always been within her, waiting for the right moment—just like the comet that once streaked across the heavens.
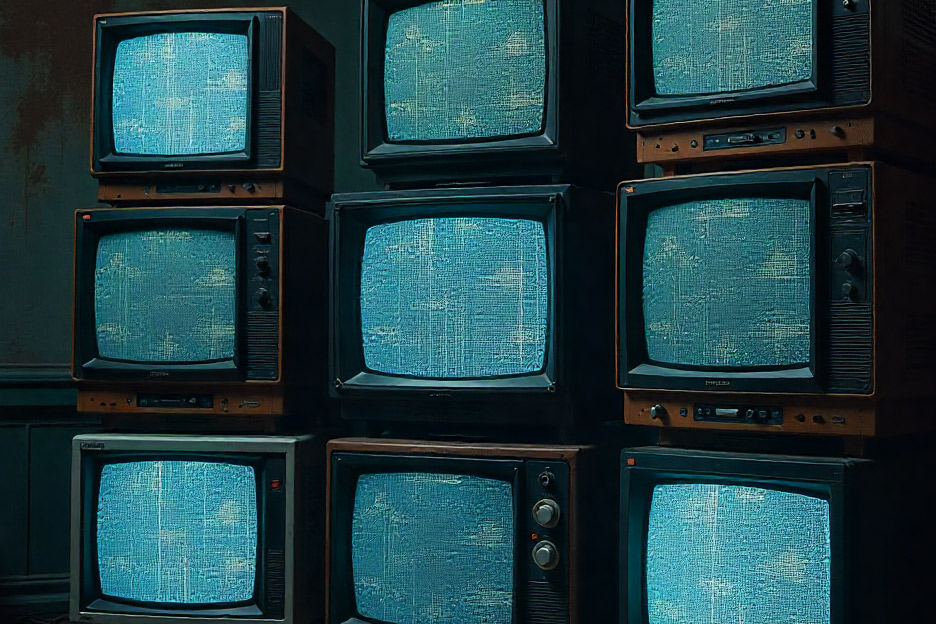
The screen flickered, then displayed A flood of files spilled onto the desktop—software executables, license files, and a single, encrypted PDF titled “The Last Key.pdf.”
Chapter 2 – The Comet’s Whisper
Maya uploaded the KMSAuto portable package, stripped of any illegal activation modules, and paired it with an open‑source license manager she’d built herself. She included a README that echoed her uncle’s riddles, encouraging users to explore, learn, and contribute.
She opened the notebook again, flipping to a page titled The entry read: “The comet arrives. The key is hidden in the 10th hour. The password is the sum of the digits of the date, multiplied by the hour we watched.” Maya stared at the numbers. The comet’s date was July 14, 2014—07/14/2014. Adding the digits: 0+7+1+4+2+0+1+4 = 19 . The hour they watched: 10 (10:17 PM). Multiplying gave 190 . She typed 190 into the password field. kmsauto net 2016 v 1.4 9 portable password
She typed into the prompt. The screen pulsed, and a new file appeared: “License_Unlock.key.” Opening it revealed a simple text string: “ACTIVATED – 2026‑04‑14” Maya realized the software wasn’t just a tool for illicit activation; it was a relic of her uncle’s attempt to create an open‑source licensing system for developers who couldn’t afford commercial solutions. He’d hidden the real “key” behind a series of puzzles, ensuring only those who truly understood the spirit of sharing and ingenuity could access it.
She opened the server’s side panel and discovered a small, weathered flash drive labeled Plugging it into the laptop, she used the KMSAuto portable app to run a diagnostic script. The program displayed a string of hexadecimal code, then a prompt: “Enter activation seed:” Maya remembered another line from the notebook, scribbled under the comet entry: “The seed is the number of days between the comet and the day we built the server.” She flipped forward to a page titled “Server Build Log – 08/02/2015.” The entry noted the server’s completion date as August 2, 2015. She calculated the days between July 14, 2014, and August 2, 2015— 384 days. In the attic, the laptop still hummed, now
Inside the PDF, a handwritten note glowed in a faint digital watermark: “You have unlocked the tool, but the true key lies elsewhere. The portable version is merely a vessel. The real activation lies in the code hidden within the firmware of the old server in the basement. Find the ‘Heart of the Machine,’ and you will awaken the legacy.” Maya’s heart raced. She descended into the basement, the air thick with the scent of old wiring and rust. In the corner stood a massive, dust‑coated server rack—an antiquated mainframe that had once powered her uncle’s fledgling software firm.